The Arrest That Shook Silicon Valley
On March 19, 2026, federal agents arrested Wally Liaw, the 71-year-old cofounder of Supermicro, at his home in California. The Department of Justice unsealed an indictment alleging that Liaw had orchestrated the largest export control violation in United States history, diverting an estimated $2.5 billion worth of artificial intelligence servers to Chinese buyers in violation of strict U.S. sanctions. The arrest sent shockwaves through Silicon Valley, wiping out more than $6 billion in market value from Supermicro’s stock within hours as shares plummeted 33% in a single trading session.
The charges against Liaw, who served as Senior Vice President of Business Development and sat on the company’s board, represent a stunning fall from grace for the entrepreneur who helped build Supermicro from a San Jose startup into a global server manufacturing giant. According to federal prosecutors, Liaw worked with two accomplices, Taiwan-based sales manager Ruei-Tsang Chang and contractor Ting-Wei Sun, to funnel restricted Nvidia GPUs through an unnamed Southeast Asian intermediary company between 2024 and early 2026. While Supermicro itself was not named as a defendant, the company acknowledged that the alleged scheme involved its employees and that it had placed Liaw and Chang on administrative leave while terminating its relationship with Sun.
The case exposes critical vulnerabilities in the enforcement of export controls designed to prevent advanced American technology from bolstering Chinese military capabilities. As artificial intelligence increasingly shapes modern warfare, autonomous weapons systems, and surveillance infrastructure, the U.S. government has tightened restrictions on selling high performance chips to China. Yet the Supermicro indictment reveals how easily these controls were circumvented for nearly two years through a combination of shell companies, forged documentation, and audacious physical deception.
The indictment arrives at a moment of heightened tension in the technological rivalry between Washington and Beijing. American officials have repeatedly warned that advanced semiconductors represent a strategic asset that could determine military superiority in the coming decades. The fact that billions of dollars worth of this technology flowed unchecked into China through what prosecutors describe as a tangled web of lies raises urgent questions about the effectiveness of current enforcement mechanisms and whether regulatory agencies have learned from historical precedents that date back nearly three decades.
The Mechanics of Deception
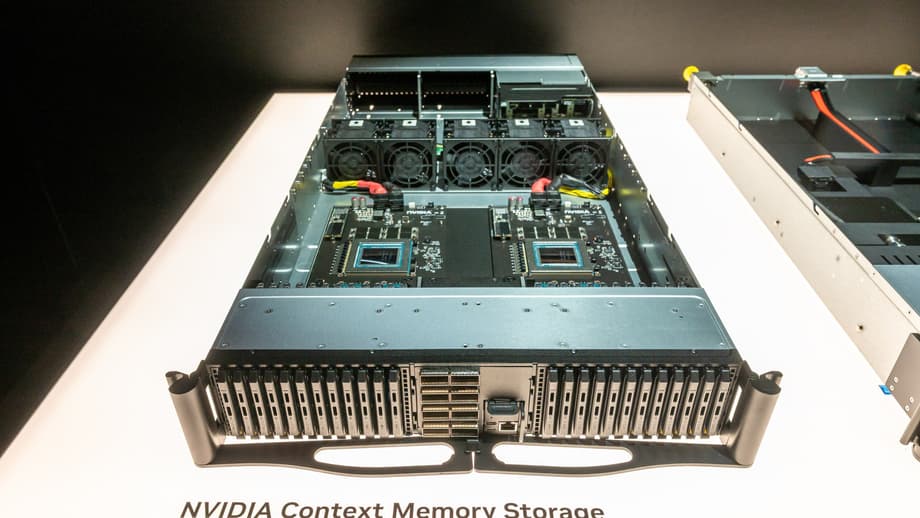
Federal prosecutors describe an operation that blended sophisticated logistics with surprisingly rudimentary deception. At the center of the scheme sat an unnamed Southeast Asian firm, referred to in court documents as “Company-1,” which functioned as the critical pass through for restricted technology. This company, incorporated outside China and nominally owned by non-Chinese nationals, placed purchase orders with Supermicro for servers equipped with Nvidia’s most advanced AI chips, including the B200 and H200 GPUs. These processors are subject to strict export controls because of their potential applications in advanced weapons development and large-scale surveillance.
The servers were assembled in the United States and shipped to Company-1’s facilities, where executives allegedly coordinated with Liaw’s team to prepare false documentation indicating the equipment would remain in Southeast Asia. Instead, workers repackaged the hardware in unmarked boxes and forwarded it to final destinations in China. To evade detection during compliance audits, the conspirators constructed an elaborate stagecraft involving thousands of dummy servers, nonworking physical replicas designed to mimic the appearance of the genuine equipment.
Surveillance footage captured the defendants preparing these decoys in warehouses, using a hair dryer to remove serial number labels from authentic server boxes and affix them to the dummy units. They then repackaged these fake servers in original manufacturer boxes to present to auditors. During one inspection by the Department of Commerce’s Bureau of Industry and Security in December 2025, contractor Ting-Wei Sun allegedly introduced himself as “Michael,” claiming to work for the law firm representing Company-1, while fielding questions from federal officers.
The scale of the operation was staggering. Between late April and mid-May 2025 alone, the defendants allegedly shipped $510 million worth of servers to China. Text messages recovered by investigators reveal Liaw’s urgency as he pressed associates to accelerate deliveries before new restrictions took effect in May 2025. “We need to speed these up before May 13!” he wrote in January 2025, later adding, “We can ship all your 512 x B200 by Feb. Let us run fast before May 13!” When news reports emerged in August 2025 about other smuggling arrests, Liaw responded with a string of sobbing face emojis before continuing to coordinate shipments.
U.S. Attorney Jay Clayton for the Southern District of New York described the operation as a systematic effort to undermine American law.
They did so through a tangled web of lies, obfuscation, and concealment, all to drive sales and generate revenues in violation of U.S. law. Diversion schemes like those disrupted today generate billions of dollars in ill-gotten gains and pose a direct threat to U.S. national security.
The brazen nature of the deception suggests a calculated assessment that export control enforcement lacked the resources or institutional persistence to detect such schemes. Even after Supermicro’s internal compliance team initiated an audit in late 2024, Chang allegedly arranged for a cooperative auditor to conduct inspections while Company-1 executives entertained the compliance officer off site. During one August 2025 audit, the officer was allegedly kept busy enjoying entertainment while the dummy servers were presented for verification.
The Southeast Asian Connection
The geographical structure of the smuggling network carries disturbing echoes of espionage tradecraft documented nearly thirty years ago. During the 1996 Chinagate investigations, the Senate Committee on Governmental Affairs documented how Chinese intelligence agencies used Southeast Asian business interests as intermediaries to funnel foreign money into American politics. A central focus of those inquiries was the Lippo Group, an Indonesian conglomerate run by the Riady family, which maintained deep financial relationships with Chinese state banks and China Resources, an entity identified by U.S. intelligence as a front for Chinese military operations.
The 1998 Senate report concluded that the use of businesses and individuals as intermediaries was becoming increasingly common among Chinese intelligence and military organizations. The strategic value of such arrangements lay precisely in their corporate location outside Chinese sovereign territory, providing plausible deniability while allowing Beijing to project financial influence through proxies that appeared legally distinct from state control.
Today’s unnamed Southeast Asian company bears striking similarities to the Lippo Group template. While Justice Department officials have not confirmed Company-1’s identity, the Singapore-based computing firm Megaspeed is actively under investigation by the Commerce Department for identical transshipment violations. Like Lippo Group before it, Megaspeed is incorporated outside China and owned by Singaporean citizens, yet reports indicate it operates as an offshoot of 7Road International, a Chinese gaming company backed by investors connected to the state. Senator Tom Cotton has publicly characterized Megaspeed as a Chinese government spin off.
The company emerged rapidly to become the single largest Southeast Asian purchaser of Nvidia chips, raising the same questions that ultimately ensnared the Riadys: Who truly controls this entity, and whose interests does it serve? The pattern suggests a deliberate resurrection of proven tradecraft, exploiting the same jurisdictional gaps that Congress identified in the late 1990s.
Supermicro’s History of Export Violations
The current scandal is not Supermicro’s first encounter with export control violations, a history that makes the recent lapses particularly troubling. In 2006, the company pleaded guilty in federal court to illegally exporting computer equipment to Iran between September 2001 and March 2003, paying $150,000 in criminal fines to the Department of Justice. In parallel civil settlements, Supermicro paid $125,400 to the Commerce Department’s Bureau of Industry and Security and an additional $179,327 to the Treasury Department’s Office of Foreign Assets Control for violations of Iranian Transactions Regulations.
The methodology employed in that case from twenty years ago mirrors the current allegations with unsettling precision. According to the 2006 charging documents, Supermicro exported servers, motherboards, and chassis from the U.S. through the United Arab Emirates, using a Dubai-based distributor as a pass through to reach Iranian end users. The company misrepresented shipper export declarations to the U.S. government, claiming no license was required when, in fact, the ultimate destination was a sanctioned nation.
Court records from 2006 indicate that Supermicro’s senior director of strategic sales knew of, or had reason to know, about the embargo on sales to Iran. Despite this institutional knowledge, the company settled the charges, implemented an in house export control program, and continued operations under the leadership of executives who remained with the firm. Howard Hideshima, who served as CFO from 2006 through 2018 and signed off on the Iran settlements, later left the company following SEC charges related to accounting irregularities in 2020.
Liaw himself left Supermicro following a 2018 accounting scandal that led to the company’s delisting from Nasdaq, only to return as an adviser in 2021 and resume a full time executive post in 2022. His rejoining the board in December 2023 placed him in a position to direct the very export control compliance he had previously violated. The sentencing memo from the 2006 Iran case stated that the fines were sufficient to deter other companies from committing similar crimes, yet the current allegations suggest that deterrence failed to prevent a repeat offense using identical tactics.
The parallel cases, separated by two decades but united by methodology, suggest a failure of corporate memory and regulatory follow through. When companies face relatively modest financial penalties for violations that generate millions in revenue, the calculation often favors risk-taking over compliance, particularly when detection appears uncertain.
Military End Users
Perhaps the most alarming aspect of the smuggling scheme involves the ultimate destination of the technology. Procurement data reviewed by Reuters reveals that four Chinese universities purchased Supermicro servers containing restricted AI chips over the past year, including two institutions with direct links to the People’s Liberation Army. These academic buyers represent a critical vector for technology transfer, as Chinese defense research increasingly relies on partnerships between military organizations and civilian universities.
Among the identified purchasers, Beihang University stands out as one of China’s Seven Sons of National Defense, a group of institutions that play central roles in aerospace, missile technology, and defense research. A March 16, 2026 procurement notice from Beihang indicates the university acquired a machine learning workstation built on a Supermicro system configured with four Nvidia A100 chips, processors explicitly banned from sale to China since 2022. Similarly, Harbin Institute of Technology, another Seven Sons member with documented involvement in satellite, robotics, and missile programs, procured a Supermicro system containing eight Nvidia A100s according to a July 2025 notice.
Both universities appear on U.S. export blacklists, which should theoretically prevent American companies from securing licenses to supply them. The fact that they nevertheless acquired restricted hardware through the Supermicro diversion scheme illustrates how sanctions evasion undermines the specific intent of U.S. national security policy. Additional tender documents reveal that at least two other military-linked universities attempted similar purchases during 2025, though it remains unclear whether these transactions were completed.
The consequences extend beyond academic research. Jacob Feldgoise, a senior data research analyst at Georgetown University’s Center for Security and Emerging Technology, notes that advanced AI computing power may in turn help improve China’s weapons design and testing, military planning and logistics, autonomous weapons systems, or surveillance. As China develops increasingly sophisticated military AI applications, including autonomous combat drones and predictive maintenance systems for naval fleets, access to American-designed chips provides capabilities that domestic Chinese semiconductor manufacturing cannot yet match.
The House Select Committee on the Chinese Communist Party has characterized such smuggling as a pervasive threat to American security. Chairman John Moolenaar noted in recent testimony that Chinese companies are willing to buy what they can, and steal what they cannot, to advance their AI ambitions, building billion-dollar supercomputing facilities in Malaysia and accessing them remotely while simultaneously engaging in outright chip smuggling.
Market Disruption
The criminal crackdown has produced immediate economic shockwaves across the global semiconductor market, fundamentally altering the supply dynamics for advanced AI hardware in China. Following Liaw’s arrest in March 2026, prices for Nvidia’s B300 servers, which house eight B300 GPUs and rank among the most powerful systems for AI inference tasks, nearly doubled on the Chinese gray market. Industry sources indicate the servers now command approximately 7 million yuan, roughly $1 million per unit, compared to $550,000 in the United States.
The price surge reflects a scarcity premium created by the sudden constriction of black market supply channels. Prior to the indictment, Chinese technology companies relied heavily on transshipment through Southeast Asia to access hardware they could not purchase directly due to export restrictions. The Supermicro case exposed the operational details of this pipeline, causing brokers and logistics providers to curtail activities as enforcement risks escalated dramatically.
Chinese AI firms now face a precarious balancing act. Despite Beijing’s official discouragement of purchasing American chips in favor of domestic alternatives like those produced by Huawei, demand for Nvidia hardware remains insatiable. Chinese AI models nearly tripled their share of global token usage to 32% in March 2026 from 5% the previous year, according to Morgan Stanley research, driving unprecedented demand for inference-capable hardware. Companies including MiniMax, Zhipu, and Alibaba’s Qwen reported token usage increases of six to sevenfold between December 2025 and March 2026.
For many Chinese firms, the risk of holding restricted hardware directly on their balance sheets has become untenable, prompting a shift toward rental arrangements costing as much as 190,000 yuan monthly on one year contracts. Yet even these prices may prove unsustainable as supply tightens further. The Trump administration’s recent requirement that Nvidia share 15% of revenue from licensed China sales with the U.S. government, combined with ongoing delays in approving H200 shipments despite theoretical clearance, has created an environment of extreme uncertainty.
Nvidia maintains that it does not support diverted systems and warns that unlawful diversion is a recipe for failure as systems grow more complex. Nevertheless, the company retains an estimated 55% market share in China’s AI chip sector, a dominance that persists despite the legal prohibitions on its most advanced products.
The Investigation Expands
Supermicro now faces a complex crisis extending far beyond the criminal charges against its former executives. The company has launched an independent investigation led by board members Scott Angel and Tally Liu, retaining outside counsel from Munger, Tolles and Olson and consultancy AlixPartners to review its Global Trade Compliance Program. Simultaneously, multiple class action securities lawsuits have emerged, covering the period from April 30, 2024 through March 19, 2026, with a May 26, 2026 deadline for investors to apply as lead plaintiffs.
The reputational damage has already translated into concrete business losses. In late April 2026, Oracle reportedly canceled an order for 300 to 400 Nvidia GB300 NVL72 server racks valued at $1.1 to $1.4 billion, a move analysts directly attribute to the DOJ overhang. Additionally, supply chain reports indicate that xAI shifted business to competitors Dell and Hewlett Packard Enterprise, leaving Supermicro with excess B200 GPU inventory.
In Washington, lawmakers are moving to close the regulatory gaps exposed by the scandal. The Multilateral Alignment of Technology Controls on Hardware (MATCH) Act, advanced by the House Foreign Affairs Committee in April 2026, would require allies including the Netherlands and Japan to align their semiconductor manufacturing equipment restrictions with U.S. rules. This would cut off ASML’s remaining China sales and ban servicing of already installed machines, further constraining China’s domestic chip production capabilities.
For the defendants, the legal consequences are severe. Liaw and Sun have pleaded not guilty to charges including conspiracy to violate the Export Controls Reform Act, which carries a maximum sentence of 20 years, plus additional counts of smuggling and conspiracy to defraud the United States. Chang remains a fugitive. Whether the prosecutions will serve as the deterrent that the 2006 Iran case failed to provide remains an open question as the AI arms race between Washington and Beijing intensifies.
Key Points
- Wally Liaw, Supermicro cofounder, was arrested March 19, 2026, for allegedly diverting $2.5 billion in AI servers to China
- The scheme used an unnamed Southeast Asian company to transship restricted Nvidia chips, evading detection for nearly two years
- Defendants allegedly used dummy servers and hair dryers to swap serial number labels during government audits
- End users included Chinese universities with direct ties to the People’s Liberation Army and defense research
- Supermicro previously pleaded guilty to similar export violations involving Iran in 2006, using an identical transshipment methodology
- The scandal caused Supermicro’s stock to drop 33% in one day and doubled gray market prices for Nvidia B300 servers in China to $1 million per unit
- Congress is now advancing the MATCH Act to tighten multilateral export controls on semiconductor manufacturing equipment